Murder case "Walter Lübcke"
- Advisory work for the "Liemecke" task force
- LKA Hessen
- Press report (Spiegel) →
Areas of application: robbery, organized crime, assassinations & terrorist attacks, threats & extortion, homicide, kidnapping & missing persons, unclear circumstances.
For the examples shown below, we cannot present all findings for reasons of scope and data protection.


Depending on the relationship between perpetrator and victim, typical but also highly specific information-gathering queries can be identified. Which queries were made, when and from where — and equally importantly, which were not — can provide significant investigative leads or support or refute existing hypotheses.
It is not uncommon for current news information to be retrieved even during an act. This circumstance alone can say a great deal about conditions at the scene as well as the number of perpetrators. Particularly relevant here is the use of mobile devices, which also serve as navigation assistants on the way to the crime scene and during flight.
Queries made before and during the act are far easier to isolate than those formulated after the event has become broadly known. Even so, perpetrators can stand out after the offence through their specific knowledge and inadvertently reveal themselves.
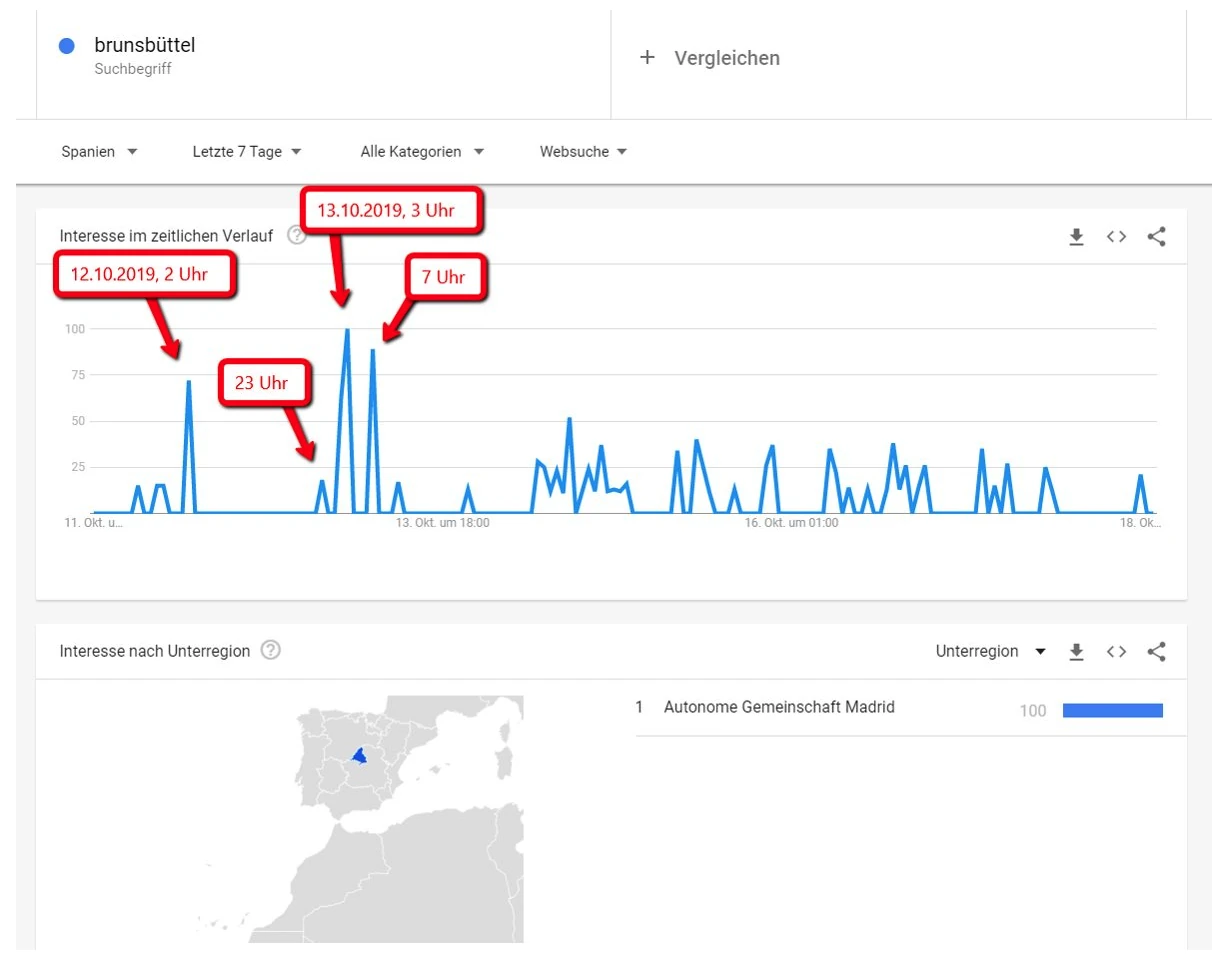
On October 14, 2019, Cora A. staged a murder-suicide scenario in the Wadden Sea. In a custody dispute over her son, she sought to conceal her flight abroad. An acquaintance recalled that Cora A. had mentioned wanting to emigrate to Spain, although it was not known of any friends or relatives there who would support her.
In fact, shortly before October 14, 2019, a striking number of queries originating in Madrid for "Brunsbüttel", Cora A.'s place of residence, can be observed. This raises the suspicion that insiders were trying to monitor the news for the expected developments.
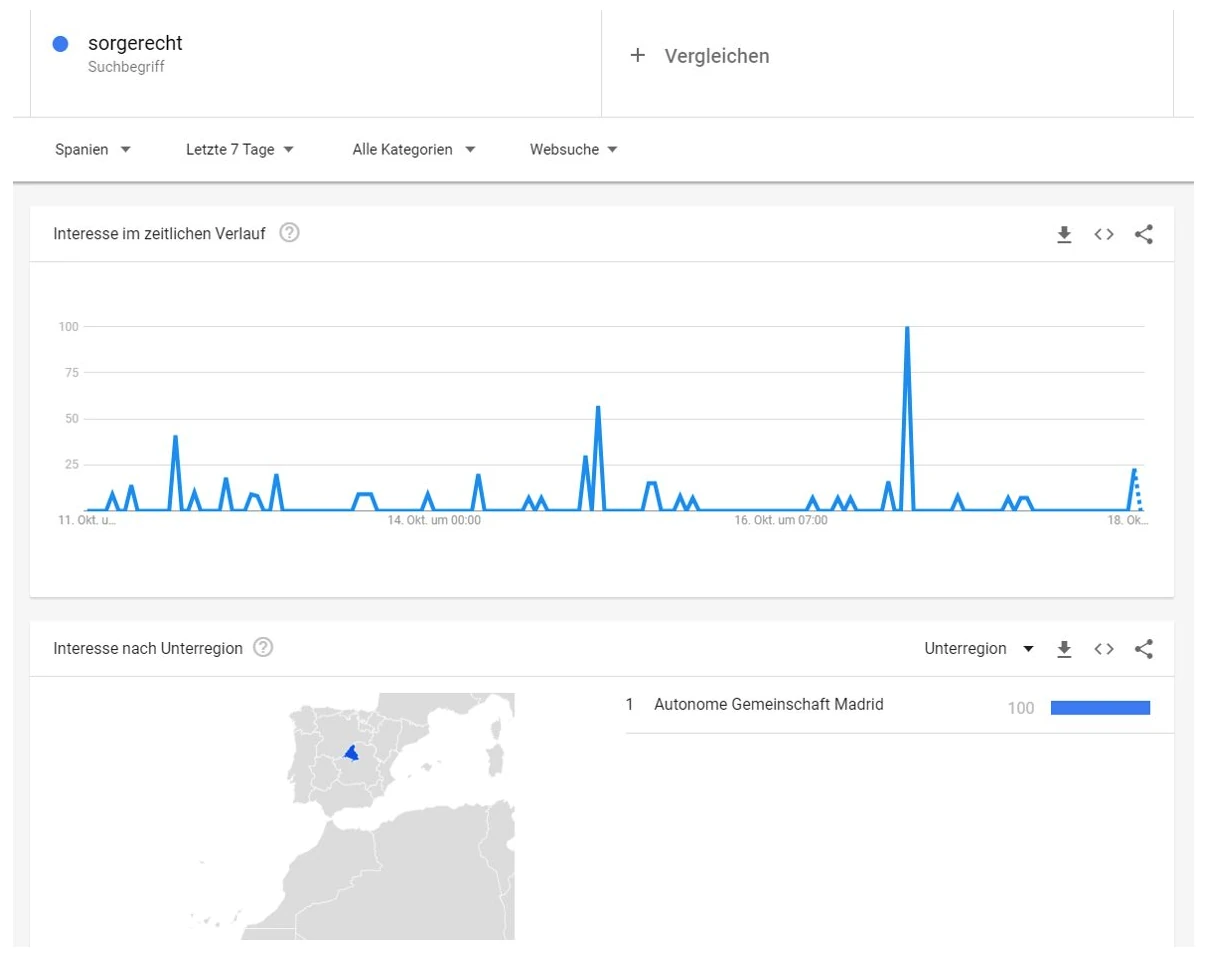
After Cora A.'s disappearance, numerous different German-language queries about custody law can be observed from Madrid. This observation suggests that Cora A. did indeed go into hiding in Madrid with her son.
In most cases, information gathering begins with the use of the search engine, which leads to a visit to at least one website. The perpetrators thereby leave a traceable trail with both the search engine and the website server.
We now determine which queries were made in the context of the act and reconstruct which search results were served at the time and were therefore potentially visited. Once these are known, they can be analyzed via embedded tracking systems such as Google Analytics, as well as via the log files.
From the data obtained, a behavioral profile can often be derived and hypotheses about the course of events and possible perpetrators can be developed. Through analysis of the log files and tracking data of the visited sources, it is even possible to determine specific personal data — such as the IP address.
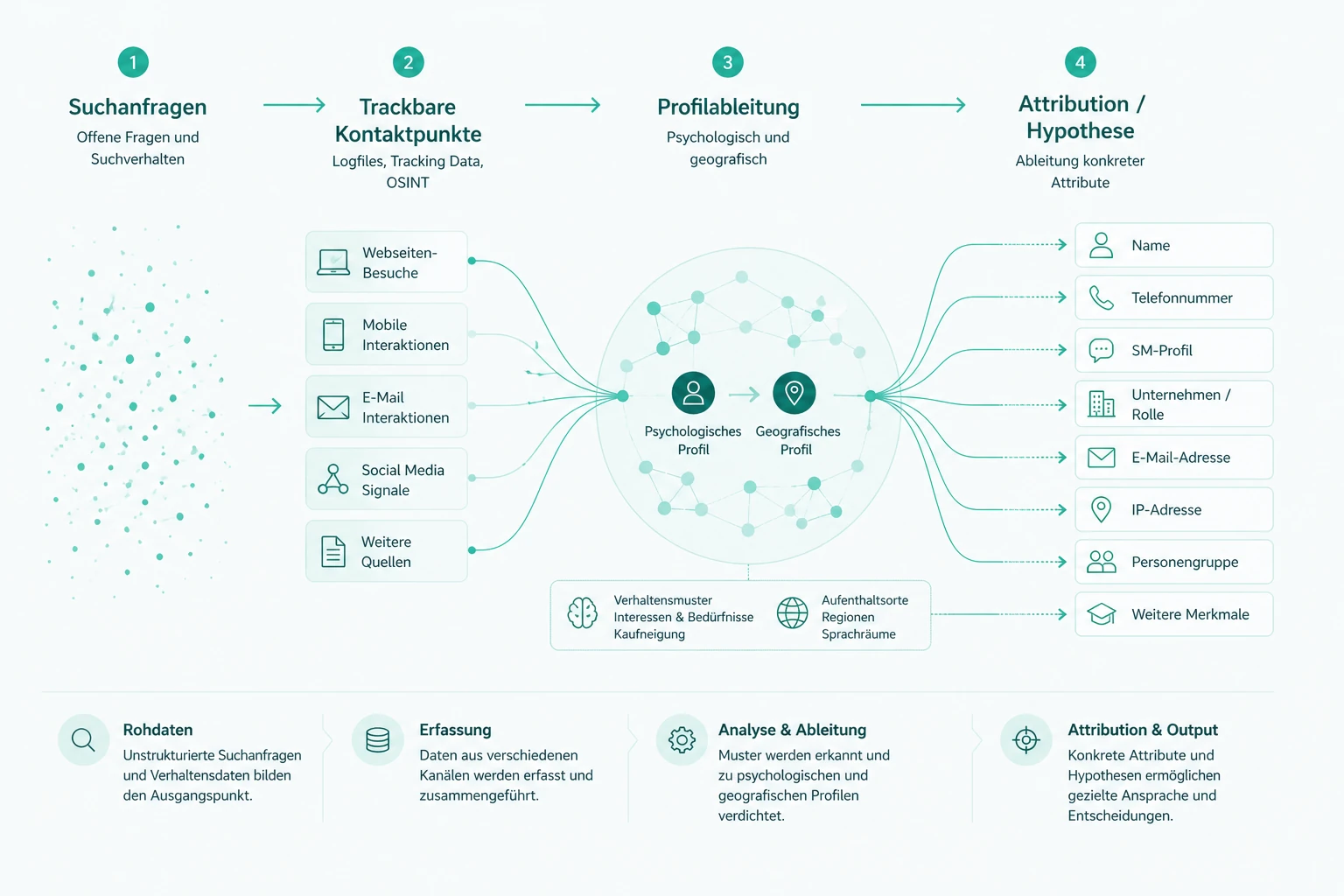
As a rule, a wide variety of different queries can be identified, all sharing a common context. The relevant queries are determined on the basis of the facts known at the time and supplemented through suitable lateral thinking models in a role-play-like manner.
At the start of an investigation, concrete hypotheses about the course of events, the origin of the perpetrators and the perpetrator-victim relationship often suggest themselves. With the help of search-profile analysis, these hypotheses can be substantiated, but also refuted. For instance, what looks like a robbery-homicide can be revealed as a planned murder.
Queries must never be viewed in isolation, but always in their temporal context. Often only this reveals the meaning of individual queries. The analysis therefore always works toward a chronological reconstruction of the information gathering.
Depending on the organizational profile of the act, movement profiles can often also be determined. These provide geographical clues to the approach to the crime scene as well as to the destination of the flight. Evaluated in temporal context, this allows a minimum and maximum radius in kilometers to be defined for where the perpetrators come from. In the best case, we even find concrete personal data.
The level of planning behind an act can also be estimated very well via analysis of the information gathering. It is possible to determine how many people knew about the act or were involved in its planning — and often also where these people come from. The use of obfuscation techniques, indicating greater professionalism, also becomes apparent.
There are perpetrators and perpetrator groups who, for various reasons, communicate via social-media channels such as Facebook or Telegram. These channels, along with all other open-source intelligence data sources, are therefore likewise included in the analysis.
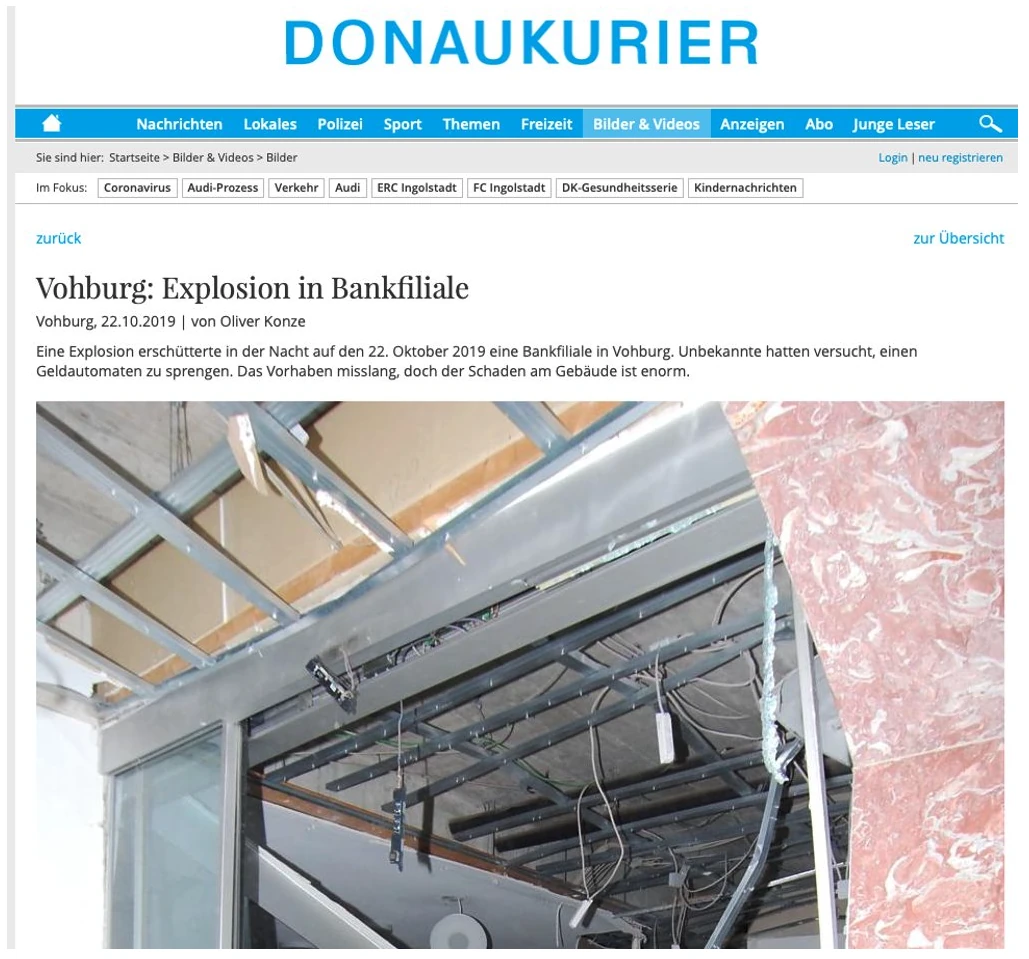
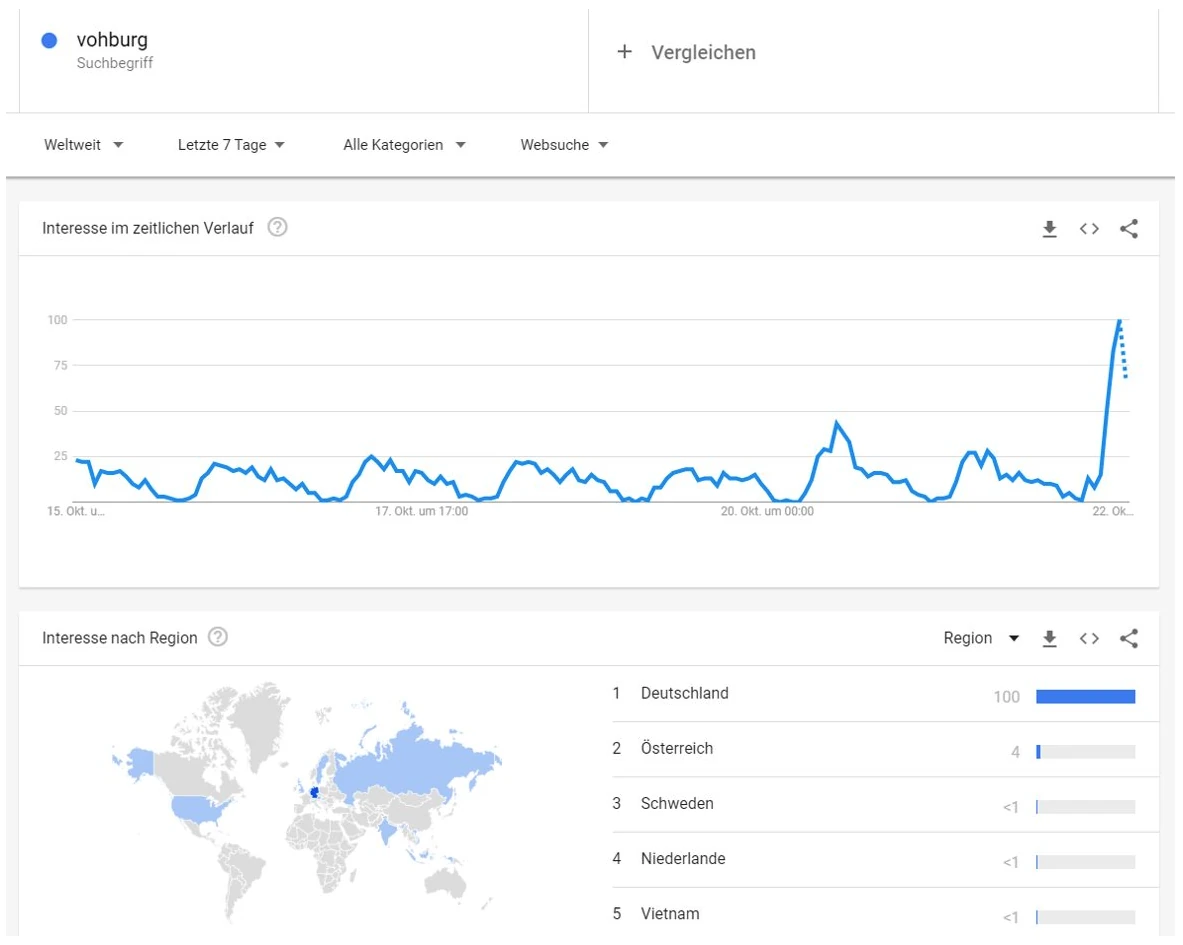
On October 22, 2019, an ATM was blown up around 3 a.m. in Vohburg, an hour's drive north of München.
Shortly before midnight we find a strikingly large number of queries for the Vohburg ZIP code 85088. At least a large share apparently originates from München, or rather a routing hub assigned to it.
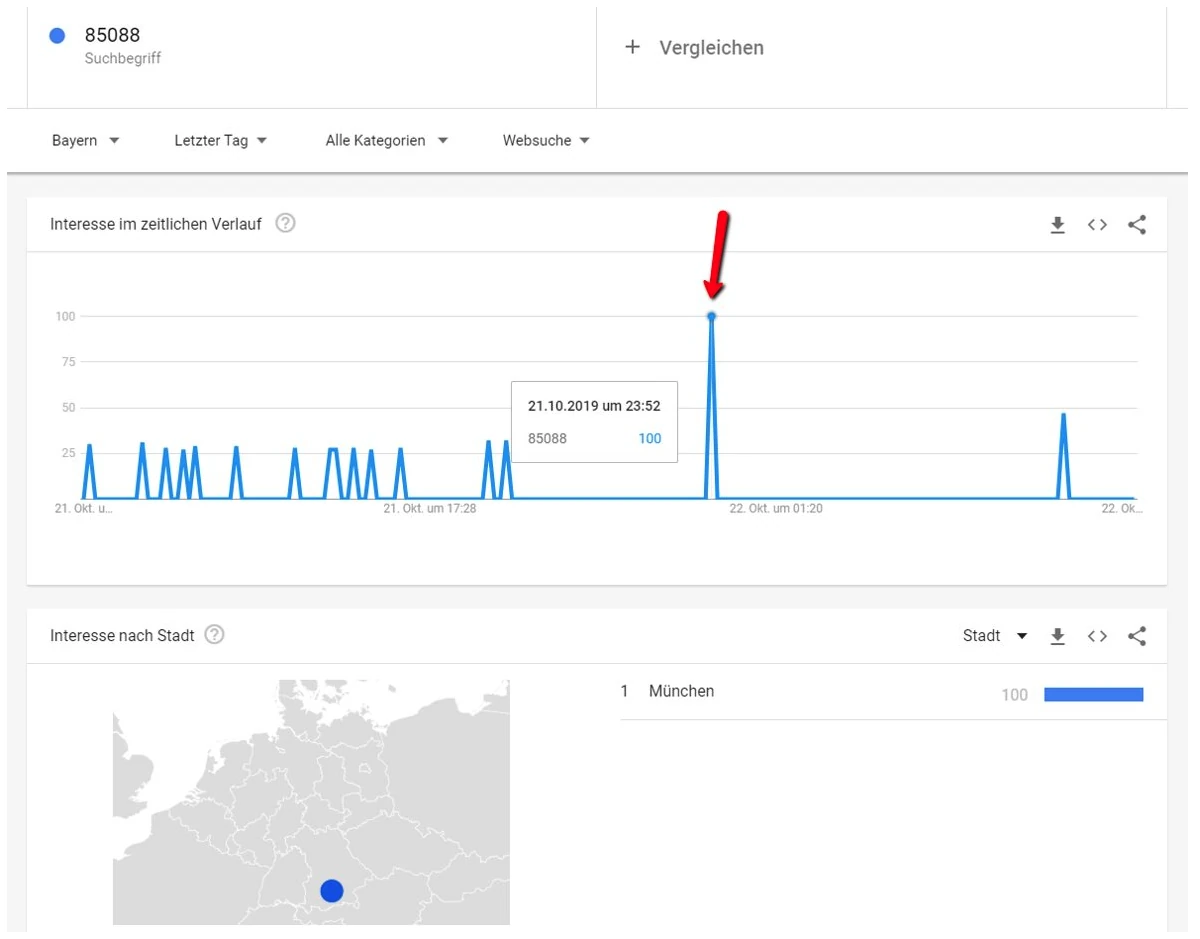
Immediately after the act, queries for a Munich ZIP code can be observed. This implies a physical movement of the perpetrators from München to Vohburg and back. The temporal frame is also plausible.
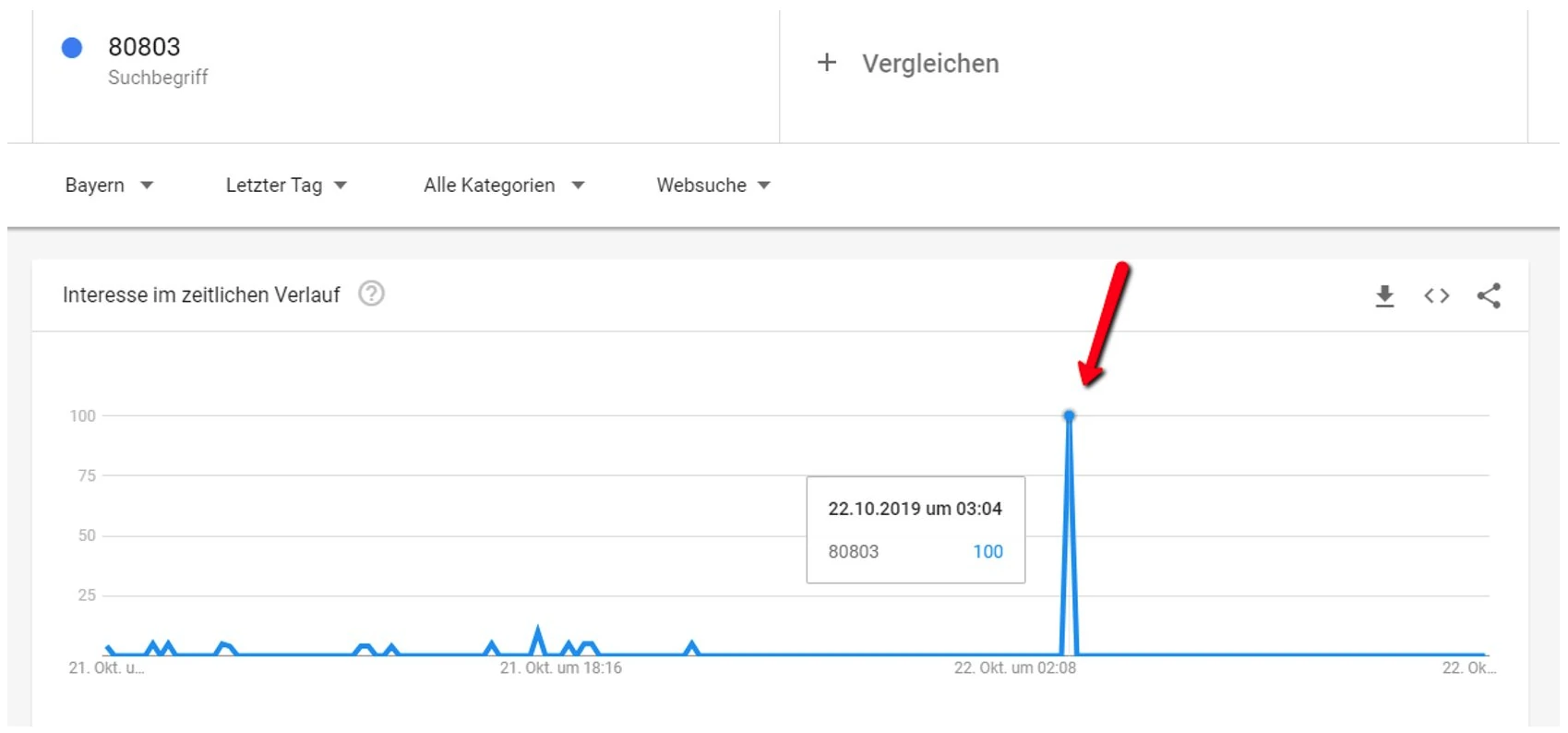
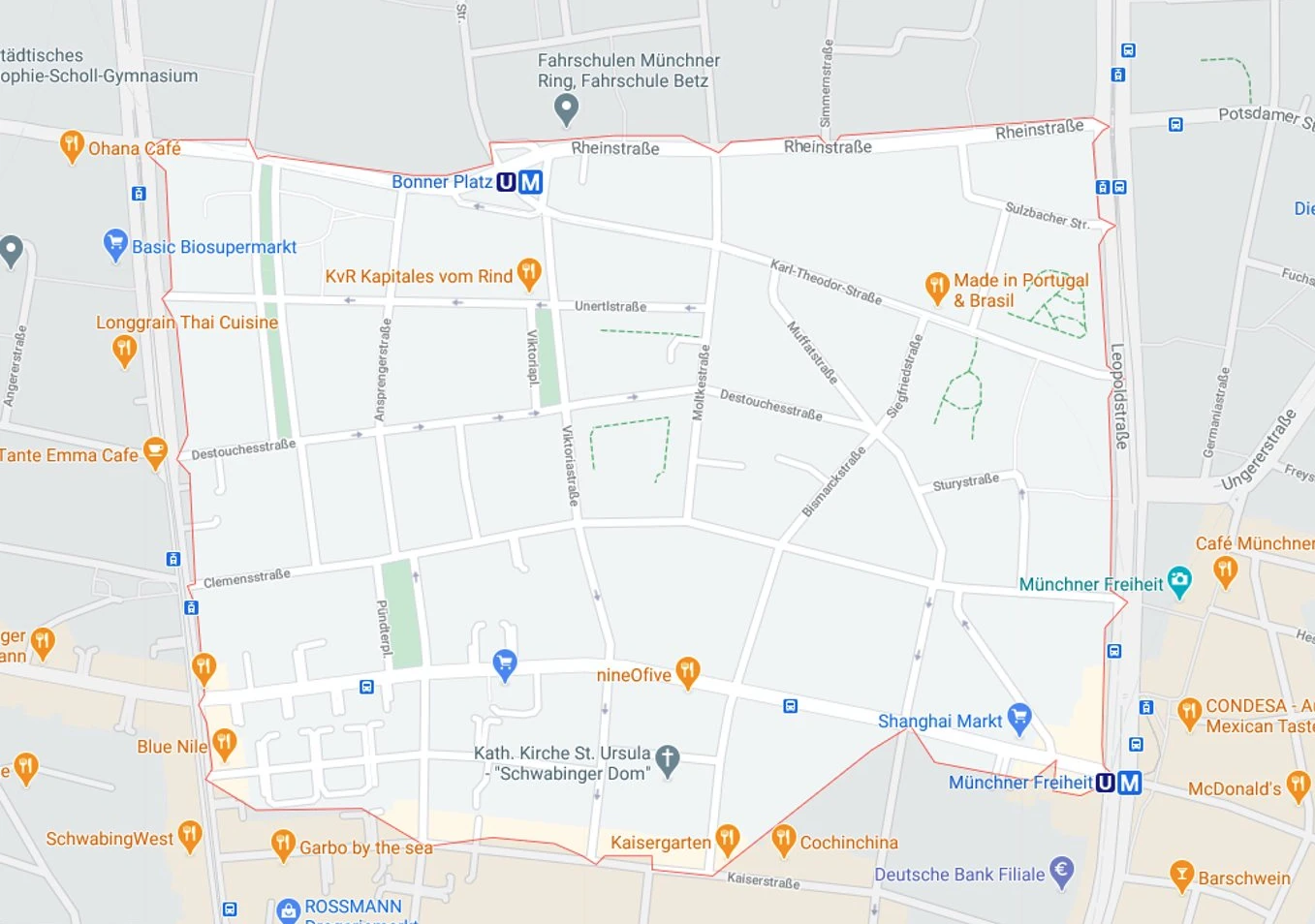
With the identified ZIP code 80803 we can derive a hypothesis about the origin of the perpetrators.
Also interesting is the observation that obfuscation techniques apparently were used in the searches for "Vohburg". It seems rather unlikely that this quiet town was queried so often in Russia, Vietnam or India. This points to a structured, organized approach.
The highest data quality is obtained within a window of up to 4 hours after the act — temporal resolution down to the minute. A more practical window is up to 24 hours, within which queries can still be pinpointed to within 8 minutes. It should be borne in mind that the planning phase — i.e. the time before the act — also represents a particular investigative window.
Beyond 24 hours but within 7 days of the act, Google provides search-volume data on a time grid rounded to the hour. This is sufficient for many investigations, since the completeness and quality of the data have not yet decreased significantly. Within this window, log files of visited sources are also available.
After a one-week window has elapsed, reconstruction options are significantly reduced. Even so, investigative leads and information fragments can often still be used, for instance from tracking systems installed on the website. The case of Madeleine McCann, abducted in 2007, shows that even after a long time, salient information can still be secured. Overall, the data reaches back to 2004.
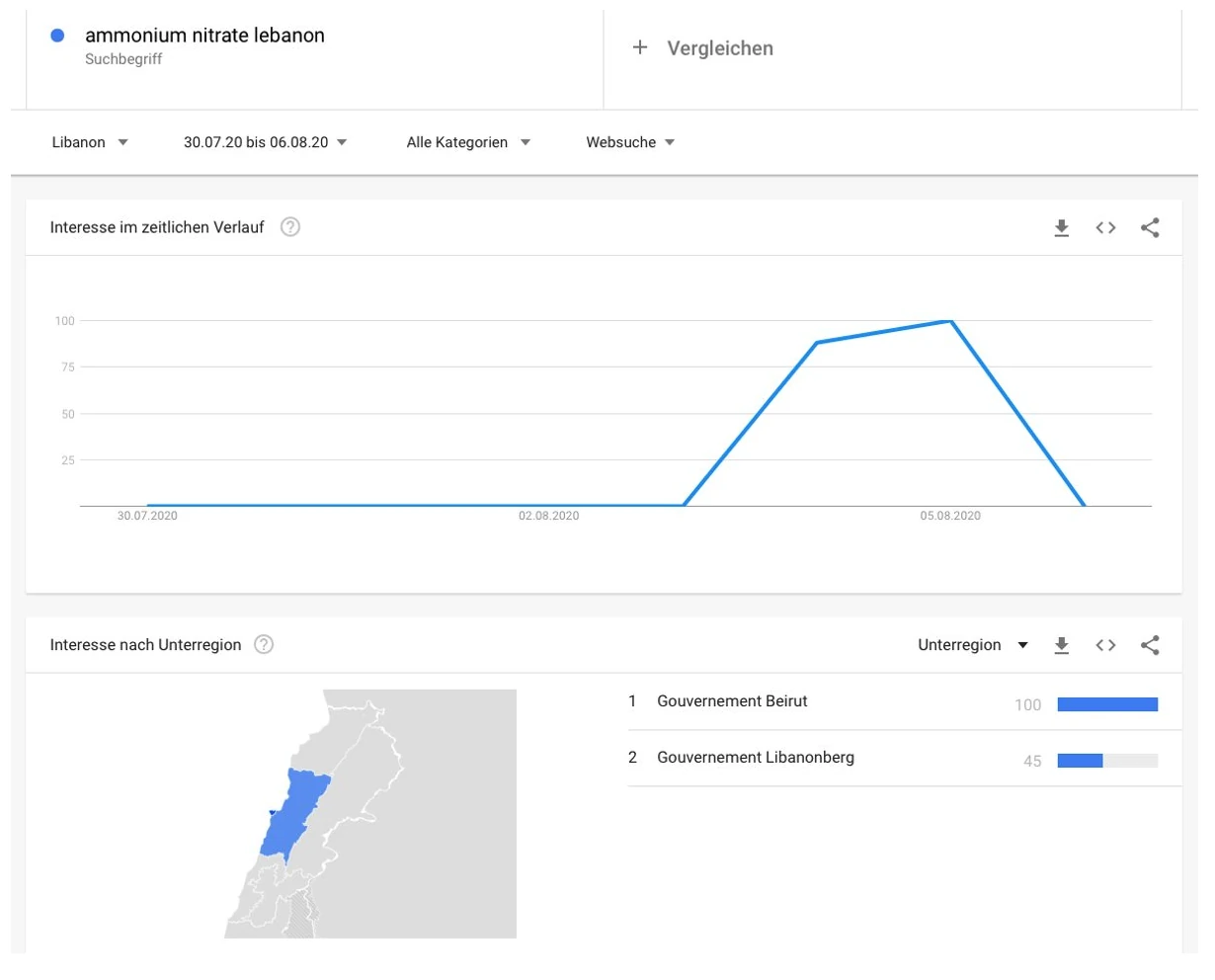
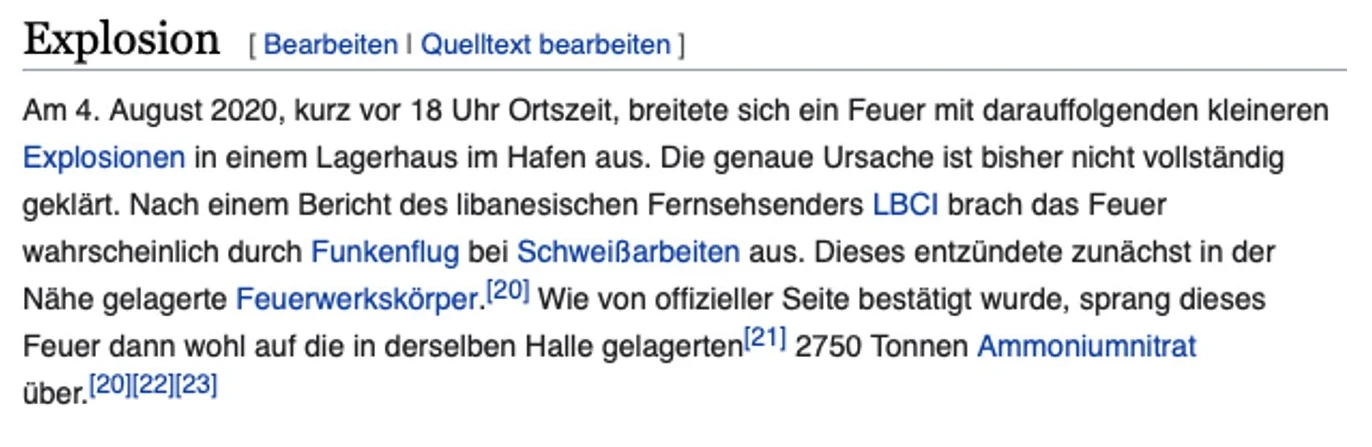
On August 4, 2020, Beirut was rocked by a very powerful explosion around 6 p.m. (5 p.m. German time).

Apparently welding work had caused sparks that triggered the explosion (source: Wikipedia).
Data secured immediately after the events, however, show striking queries about the stored substance responsible for the explosion already days beforehand. This observation could call into question whether this was really an accident or rather an attack.
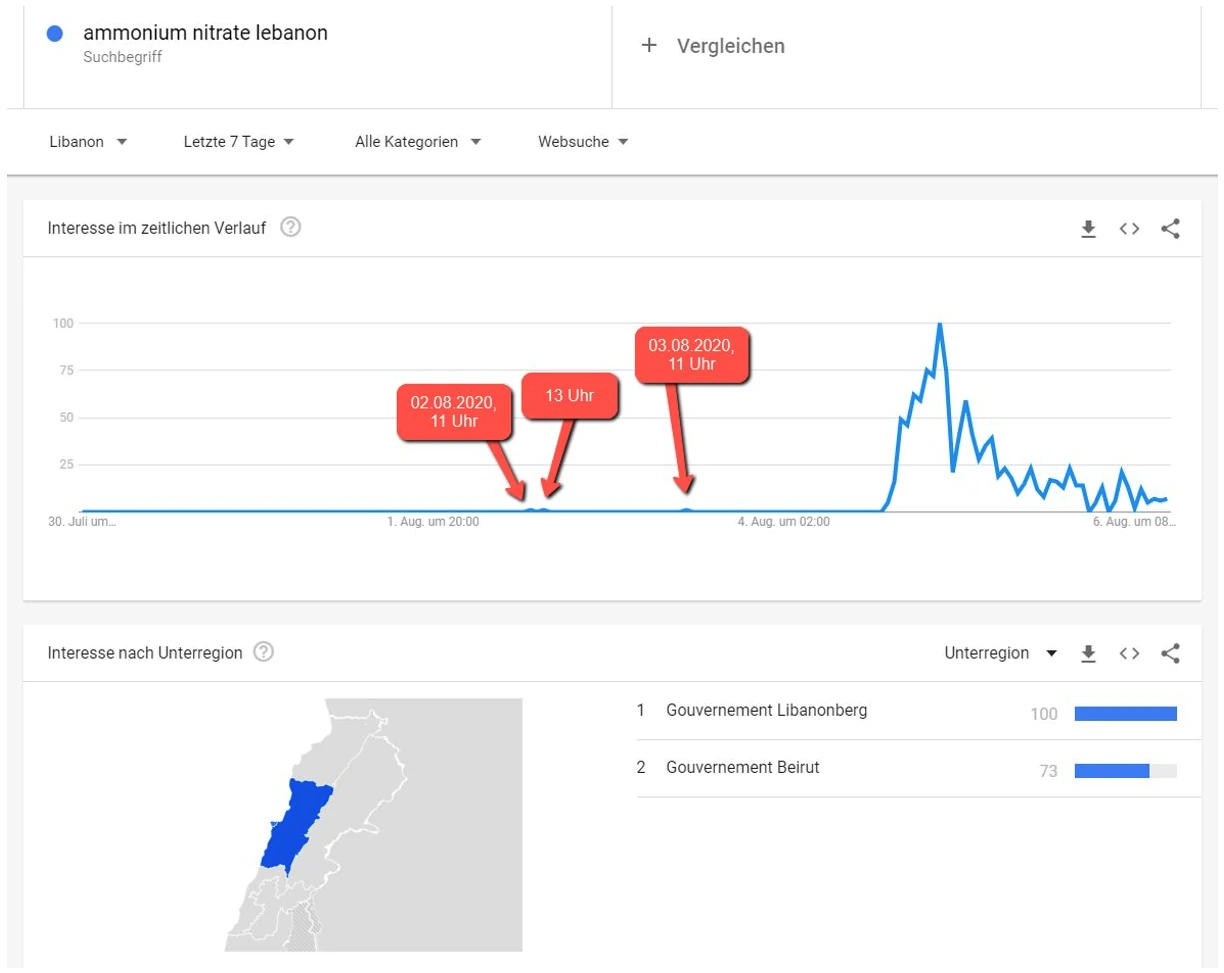
If we observe the exact same time window a few months later, the striking queries can no longer be found. The data quality has dropped markedly. An analysis based only on this later data would therefore arrive at completely different conclusions.